Notification
This report is provided "as is" for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise.
This document is marked TLP:CLEAR--Disclosure is not limited. Sources may use TLP:CLEAR when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:CLEAR information may be distributed without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.cisa.gov/tlp .
Summary
Description
CISA received 18 files for analysis from a forensic analysis engagement conducted at a Federal Civilian Executive Branch (FCEB) agency.Threat Actors Exploit Progress Telerik Vulnerability in U.S. Government IIS Server .
Download the PDF version of this report:
For a downloadable copy of IOCs, see
Submitted Files (18)
11415ac829c17bd8a9c4cef12c3fbc23095cbb3113c89405e489ead5138384cd (1597974061[.]4531896[.]png)
144492284bcbc0110d34a2b9a44bef90ed0d6cda746df6058b49d3789b0f851d (1666006114[.]5570521[.]txt)
508dd87110cb5bf5d156a13c2430c215035db216f20f546e4acec476e8d55370 (xesmartshell[.]tmp)
707d22cacdbd94a3e6dc884242c0565bdf10a0be42990cd7a5497b124474889b (1665130178[.]9134793[.]dll)
72f7d4d3b9d2e406fa781176bd93e8deee0fb1598b67587e1928455b66b73911 (1594142927[.]995679[.]png)
74544d31cbbf003bc33e7099811f62a37110556b6c1a644393fddd0bac753730 (1665131078[.]6907752[.]dll)
78a926f899320ee6f05ab96f17622fb68e674296689e8649c95f95dade91e933 (1596686310[.]434117[.]png)
833e9cf75079ce796ef60fc7039a0b098be4ce8d259ffa53fe2855df110b2e5d (1665128935[.]8063045[.]dll)
853e8388c9a72a7a54129151884da46075d45a5bcd19c37a7857e268137935aa (1667466391[.]0658665[.]dll)
8a5fc2b8ecb7ac6c0db76049d7e09470dbc24f1a90026a431285244818866505 (1596923477[.]4946315[.]png)
a14e2209136dad4f824c6f5986ec5d73d9cc7c86006fd2ceabe34de801062f6b (1665909724[.]4648924[.]dll)
b4222cffcdb9fb0eda5aa1703a067021bedd8cf7180cdfc5454d0f07d7eaf18f (1665129315[.]9536858[.]dll)
d69ac887ecc2b714b7f5e59e95a4e8ed2466bed753c4ac328931212c46050b35 (1667465147[.]4282858[.]dll)
d9273a16f979adee1afb6e55697d3b7ab42fd75051786f8c67a6baf46c4c19c2 (SortVistaCompat)
dedf082f523dfcb75dee0480a2d8a087e3231f89fa34fcd2b7f74866a7b6608f (1665214140[.]9324195[.]dll)
e044bce06ea49d1eed5e1ec59327316481b8339c3b6e1aecfbb516f56d66e913 (1667465048[.]8995082[.]dll)
e45ad91f12188a7c3d4891b70e1ee87a3f23eb981804ea72cd23f1d5e331ff5a (1596835329[.]5015914[.]png)
f5cafe99bccb9d813909876fa536cc980c45687d0f411c5f4b5346dcf6b304e4 (1665132690[.]6040645[.]dll)
Additional Files (6)
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415 (small[.]aspx)
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad (XEReverseShell[.]exe)
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2 (xesvrs[.]exe)
5cbba90ba539d4eb6097169b0e9acf40b8c4740a01ddb70c67a8fb1fc3524570 (small[.]txt)
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f (XEReverseShell[.]exe)
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c (Multi-OS_ReverseShell[.]exe)
Domains (3)
hivnd[.]com
xegroups[.]com
xework[.]com
IPs (4)
137[.]184[.]130[.]162
144[.]96[.]103[.]245
184[.]168[.]104[.]171
45[.]77[.]212[.]12
Findings
144492284bcbc0110d34a2b9a44bef90ed0d6cda746df6058b49d3789b0f851d
Tags
wiper
Details
Name
1666006114.5570521.txt
Size
12288 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
8e33e1e407fc9ff537b63be3ab78cb40
SHA1
1228a2269610fcd20d6b0cf982b759b4c7612f34
SHA256
144492284bcbc0110d34a2b9a44bef90ed0d6cda746df6058b49d3789b0f851d
SHA512
d5b0ee2931ada3f3c51a201433e9b907d4efdbb88fb3825613f6ed16e80be2ddb4d23ccc8ee5d1af14ee13045b6d80f2909d007d016c8cf0436b0462fcb92732
ssdeep
96:/sJBSe0UzgkuQZR39ZoUnXpxs1bc9m4oJ1nbBeFsPW0dfk/QSvlWHaRA3naHrt/y:/ESvLkKUXpxsNcgb9pvRYGsrhUU/HkY
Entropy
4.610852
Antivirus
No matches found.
YARA Rules
rule CISA_10413062_04 : wiper compromises_data_availability
rule CISA_10413062_07 : wiper compromises_data_availability
ssdeep Matches
No matches found.
Description
This file is a malicious .NET DLL, which contains malicious unmanaged 64-bit Intel code. This DLL deletes files that end in ".dll" from C:\windows\temp.
e044bce06ea49d1eed5e1ec59327316481b8339c3b6e1aecfbb516f56d66e913
Tags
information-stealer
Details
Name
1667465048.8995082.dll
Size
13312 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
f6f47911ac32afd786a765dcb1f26722
SHA1
533bfde3f801f7e1c7b519dcb07e7f21e6546306
SHA256
e044bce06ea49d1eed5e1ec59327316481b8339c3b6e1aecfbb516f56d66e913
SHA512
6cbc2e9114dba4f5ba37dbeec3de5610abfc2a23e2c3d74b5943d88392235fe741dca73bb560bb33e366d2d780708e7b7dc40186c46148b45761bb32034c67ff
ssdeep
192:UqLqxAm19p0WSLQs68UbUA+RaYlLWcTU/:zIAkXON6LUAY4cT
Entropy
4.929398
Antivirus
No matches found.
YARA Rules
rule CISA_10413062_01 : exfiltrates_data
rule CISA_10413062_06 : exfiltrates_data
ssdeep Matches
No matches found.
Relationships
e044bce06e....
Connected_To
45[.]77[.]212[.]12
Description
This file is a malicious .NET DLL, which contains malicious unmanaged 64-bit Intel code. Loading this DLL will send "+_+_+" to 45[.]77[.]212[.]12 over port 443. Then, C:\inetpub\temp, D:\inetpub\temp, and E:\inetpub\temp are scanned recursively for files that end in .config.
45[.]77[.]212[.]12
Tags
command-and-control
Ports
Whois
NetRange: 45[.]76[.]0[.]0 - 45[.]77[.]255[.]255
Relationships
45[.]77[.]212[.]12
Connected_From
e044bce06ea49d1eed5e1ec59327316481b8339c3b6e1aecfbb516f56d66e913
45[.]77[.]212[.]12
Connected_From
d69ac887ecc2b714b7f5e59e95a4e8ed2466bed753c4ac328931212c46050b35
45[.]77[.]212[.]12
Connected_From
853e8388c9a72a7a54129151884da46075d45a5bcd19c37a7857e268137935aa
45[.]77[.]212[.]12
Connected_From
a14e2209136dad4f824c6f5986ec5d73d9cc7c86006fd2ceabe34de801062f6b
Description
This IP was utilized by multiple malicious applications in this report as a C2 server. It is utilized by the malware to send status information from commands executed on system, as well as a location to exfiltrate sensitive system and network information.
d69ac887ecc2b714b7f5e59e95a4e8ed2466bed753c4ac328931212c46050b35
Tags
information-stealer
Details
Name
1667465147.4282858.dll
Size
13312 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
cd6c11f89b392988e0de3ffe048a561b
SHA1
6a2291e077c476d03ffe98b6f3228c82c5b451e4
SHA256
d69ac887ecc2b714b7f5e59e95a4e8ed2466bed753c4ac328931212c46050b35
SHA512
a31374d97f0b4e32d14a839b7e943f2385820cd4174114675fa217b921bbbd92792a829ccef9c4bdbc01efa5d8f654a5684527ada02b415fe5bc04384934086c
ssdeep
192:U7LqxAm19p0WSLQs68UbUA+RR6uVLWcTU/:WIAkXON6LUA2IcT
Entropy
4.931255
Antivirus
No matches found.
YARA Rules
rule CISA_10413062_01 : exfiltrates_data
ssdeep Matches
No matches found.
Relationships
d69ac887ec....
Connected_To
45[.]77[.]212[.]12
Description
This file is a malicious .NET DLL, which contains malicious unmanaged 64-bit Intel code. The file has the same functionality as "1667465048[.]8995082[.]dll" (e044bce06e...).
853e8388c9a72a7a54129151884da46075d45a5bcd19c37a7857e268137935aa
Tags
information-stealer
Details
Name
1667466391.0658665.dll
Size
12800 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
cece36ea4e328f093517ff68d0ed085c
SHA1
02df1d2e88a8317215e34cb248b5a0f7a0af830a
SHA256
853e8388c9a72a7a54129151884da46075d45a5bcd19c37a7857e268137935aa
SHA512
db34c0e32d87ee1f83d0805edba0af32385e673ded3e4215ae2b4d6e87594192e16def9284604cd88a88a0421a27f14afe0b1a54a40541cfef51e9ad2d1ad25f
ssdeep
96:9aIum+vgUGsgUxbCfVYfqAs1eAQ6vCJJ4n6qsPYsCx5lAPRa7U2eOvTyYiiZfPRa:9I8nBUffqAsMu6gxQH2eCkmXNnnUU/l
Entropy
4.659841
Antivirus
No matches found.
YARA Rules
rule CISA_10413062_02 : information_stealer information_gathering
rule CISA_10413062_08 : information_stealer information_gathering
ssdeep Matches
No matches found.
Relationships
853e8388c9....
Connected_To
45[.]77[.]212[.]12
Description
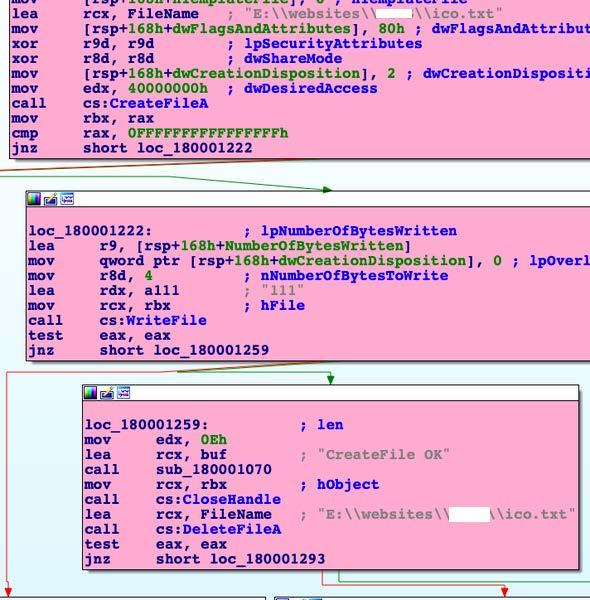
This file is a malicious .NET DLL, which contains malicious unmanaged 64-bit Intel code. Loading this DLL will send "+_+_+" to 45[.]77[.]212[.]12 over port 443. The DLL will then create E:\websites\<redacted>\ico[.]txt and write “111” to that file. If there was an error creating the file, “CreateFile Error code: {Error_Code}” will be sent to the IP and execution ends. If there was an error writing to the file, “WriteFile Error code: {Error_Code}” will be sent to the IP and execution ends. If there are no errors, “CreateFileA OK” will be sent. The DLL will then delete E:\websites\<redacted>\ico[.]txt. If successful, “DeleteFileA OK” will be sent to the IP. If there was an error “DeleteFileA failed” will be sent to the IP.
Screenshots
Figure 1 - This code illustrates the malware attempting to create a file on the targeted system within the E:\\websites\ directory. This appears to be a test to ensure the remote operator can remotely install web application code onto the target.
a14e2209136dad4f824c6f5986ec5d73d9cc7c86006fd2ceabe34de801062f6b
Tags
trojan
Details
Name
1665909724.4648924.dll
Size
13312 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
bad264a0529cacea56a845bd9d11d55b
SHA1
76df69648631be3c6262d6e51f066d397563f097
SHA256
a14e2209136dad4f824c6f5986ec5d73d9cc7c86006fd2ceabe34de801062f6b
SHA512
a60338de4fada1967776a8a060cb495140fe6a09291a4ffb3326e72c6c6f2312d5bd68a5e5f63aef8928468fe5f31a4cedf0ec8703781b4e4cb577da1789d005
ssdeep
192:Ub+8o8o9a0ybzz3O8dMFoTaVyiD4TaZNU/4E4:U6NybG8duvVZNZJ
Entropy
4.637910
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
a14e220913....
Connected_To
45[.]77[.]212[.]12
Description
This file is a malicious .NET DLL, which contains malicious unmanaged 64-bit Intel code. Static analysis indicates that the primary purpose of this code is to obtain a copy of the targeted system's TCP connection table via the GetTcpTable API, and export it to the malware's remote C2 server 45[.]77[.]212[.]12.
Screenshots
Figure 2 - The malicious binary loading its C2 IP 45[.]77[.]212[.]12 onto the stack.
Figure 3 - The malware obtaining a copy of the targeted system's TCP connection table. Analysis indicates the TCP table will be exfiltrated to the remote C2 server.
8a5fc2b8ecb7ac6c0db76049d7e09470dbc24f1a90026a431285244818866505
Tags
droppertrojan
Details
Name
1596923477.4946315.png
Size
143872 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
7947ce86923d732e6963c79aea757036
SHA1
3489d69540a435df50e9d5d80fb59c3c3a0080b4
SHA256
8a5fc2b8ecb7ac6c0db76049d7e09470dbc24f1a90026a431285244818866505
SHA512
4f78863442191e255e58a65c01ac5ad85d78a8edfd2b08cfaa74492c9b65ff0caba17267f7f7b9a29bd006a4561e63d0007d7eef6195c65e6d956a2e55f6bb67
ssdeep
3072:C82Xor1heBTboWWziX5HxtBY42UVJhG4k6F:cXorrUbo3ez
Entropy
6.242970
Antivirus
Avira
HEUR/AGEN.1229794
Bitdefender
Gen:Variant.Tedy.146424
Emsisoft
Gen:Variant.Tedy.146424 (B)
ESET
a variant of Win64/Agent.AQS trojan
K7
Riskware ( 0040eff71 )
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
8a5fc2b8ec....
Dropped
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
Description
This artifact is a DLL that drops and executes a reverse shell utility. When the DLL is loaded, it will drop an embedded and base64 encoded payload named ‘sortcombat’ into the path C:\Windows\Temp. The program will then invoke the Windows command-line utility certutil[.]exe with the –decode option and write the new file as sortcombat[.]exe into C:\Windows\Temp. Cmd[.]exe is then invoked to execute sortcombat[.]exe.
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
Tags
backdoordecryptordroppertrojan
Details
Name
XEReverseShell.exe
Size
10752 bytes
Type
PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows
MD5
eaa579d911b8a47eaaea744d59d14708
SHA1
db086131afaec88f4a4daa23973d214d666d39c0
SHA256
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
SHA512
7b24349db93c8be641268cbbbea5c10ca29d8278817d17f461879afe6aa7ee2919201b422f7cfed3e30c8e1d4792dea10f1e5d656ca4e8360eea1a7f9956afb5
ssdeep
192:sleM/+Kcp/5wep7fJ34R+cOqlY8zury3SFj+et:XKS/zy/7Y8zUy8Vt
Entropy
5.003852
Path
C:\Windows\Temp
Antivirus
AhnLab
Trojan/Win.REVSHELL
Avira
TR/Agent.otyay
ESET
a variant of MSIL/Agent.CYN trojan
IKARUS
Trojan.MSIL.Agent
K7
Trojan ( 0056c3b91 )
NANOAV
Trojan.Win32.Generic.htepmy
Trend Micro
Trojan.74E45304
Trend Micro HouseCall
Trojan.74E45304
VirusBlokAda
TScope.Trojan.MSIL
Zillya!
Trojan.Agent.Win32.1371510
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
11d8b9be14....
Dropped_By
8a5fc2b8ecb7ac6c0db76049d7e09470dbc24f1a90026a431285244818866505
11d8b9be14....
Downloaded
5cbba90ba539d4eb6097169b0e9acf40b8c4740a01ddb70c67a8fb1fc3524570
11d8b9be14....
Connected_To
xework[.]com
Description
This artifact is a reverse shell utility with the internal name of ‘XEReverseShell[.]exe’ that is dropped by "1596923477[.]4946315[.]png" (8a5fc2b8ec...) into C:\Windows\Temp as sortcombat[.]exe. When this utility is executed it will attempt to connect to the domain xework[.]com to obtain the IP address of the C2 and port number to listen on. If no IP address or port number is obtained the program will terminate.
xework[.]com
Tags
command-and-control
Ports
HTTP Sessions
GET /masterip HTTP/1[.]1
GET /masterport HTTP/1[.]1
Whois
Domain Name: XEWORK[.]COM
Relationships
xework[.]com
Connected_From
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
xework[.]com
Connected_From
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
xework[.]com
Resolved_To
184[.]168[.]104[.]171
xework[.]com
Resolved_To
144[.]96[.]103[.]245
Description
At the time of analysis, the files "XEReverseShell[.]exe" (11d8b9be14...) and "Multi-OS_ReverseShell[.]exe" (a0ab222673...) attempted to connect to this domain.
184[.]168[.]104[.]171
Relationships
184[.]168[.]104[.]171
Resolved_To
xegroups[.]com
184[.]168[.]104[.]171
Resolved_To
hivnd[.]com
184[.]168[.]104[.]171
Resolved_To
xework[.]com
Description
At the time of analysis, the domains xework[.]com, xegroups[.]com, and hivnd[.]com resolved to this IP address.
144[.]96[.]103[.]245
Relationships
144[.]96[.]103[.]245
Resolved_To
xework[.]com
Description
The domain xework[.]com returned this IP address as the masterip for the reverse shell.
5cbba90ba539d4eb6097169b0e9acf40b8c4740a01ddb70c67a8fb1fc3524570
Tags
downloaderuploaderwebshell
Details
Name
small.txt
Size
8900 bytes
Type
ASCII text, with very long lines, with no line terminators
MD5
d75ab9cb786b6f125e4cdbc92a73fa21
SHA1
d5cdda25247c3e6f1fd099077fae156ed7bada4f
SHA256
5cbba90ba539d4eb6097169b0e9acf40b8c4740a01ddb70c67a8fb1fc3524570
SHA512
b49caa7b6fdbeba5ba8e615e9297bd52e89e2eb9af220a63064fe3479c8ffcafe21f6f446a8acb23073478284bfb8b963e223ff76baa4c1dd95e15f364579ae2
ssdeep
192:xNXm9xavX5N7R9e9WO7tAp1qTzUUCDhI5L6WrG/ht:x1my/5N7R9eO1qTwUei5baJt
Entropy
5.730812
Path
C:\Windows\Temp
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
5cbba90ba5....
Related_To
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
5cbba90ba5....
Downloaded_By
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
Description
This artifact is a base64 encoded text file that is downloaded by "XEReverseShell[.]exe" (11d8b9be14...) and decoded as small[.]aspx. Then it is placed in the path C:\Windows\Temp.
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
Tags
downloadertrojanuploaderwebshell
Details
Name
small.aspx
Size
6674 bytes
Type
HTML document, ASCII text, with CRLF line terminators
MD5
ce8481189008d7f4a685615508110d88
SHA1
2ec08e86c5605c1d5b4b979067148c5e4d334979
SHA256
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
SHA512
48e28bbc4b3f852cb050fbc2566eae1f8f4d34d2452c1855f07619f6ecbbaeb1afd5b6279273876653b5f08204a48e56fbf7eb3299973949ccd58cab05ef4611
ssdeep
192:HK9wCk78M7t/H1dRfHWgWOWPlWbDLAMEM26C9tTVUFF:QLw8EfHWgWOWPlW3LcM26C9tTOF
Entropy
5.426950
Path
C:\Windows\Temp
Antivirus
AhnLab
WebShell/ASP.Generic.S1358
Avira
BDC/ASPShell.G2
ESET
ASP/Webshell.IW trojan
IKARUS
Trojan.ASP.Agent
Trend Micro
Backdoo.994AB529
Trend Micro HouseCall
Backdoo.994AB529
YARA Rules
rule CISA_10413062_09 : trojan webshell
ssdeep Matches
No matches found.
Relationships
08375e2d18....
Related_To
5cbba90ba539d4eb6097169b0e9acf40b8c4740a01ddb70c67a8fb1fc3524570
08375e2d18....
Dropped_By
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
08375e2d18....
Dropped_By
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
08375e2d18....
Dropped_By
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
Description
This artifact is an ASPX webshell. The webshell is able to enumerate drives on the system, send, receive and delete files, and also execute incoming commands. The webshell contains an interface for easily browsing for files, directories, or drives on the system. It can sort files by size or MAC time, and allows the user to upload or download files to any directory.
78a926f899320ee6f05ab96f17622fb68e674296689e8649c95f95dade91e933
Tags
decryptordroppertrojan
Details
Name
1596686310.434117.png
Size
165376 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
d3cf1d590b2a63ae6070dd0011390f03
SHA1
395c45a16e491652b53b845cc3618cfe2c022f09
SHA256
78a926f899320ee6f05ab96f17622fb68e674296689e8649c95f95dade91e933
SHA512
728bce79d8b2c14048a9cebedcf5e3fb671f60d484405746b50de304c5739fb16cb68f6e5099bb0e85b37d7f181881257618617e55a7520eabd8d89f2ffecaa0
ssdeep
3072:gfiiSHmmxCxt1bWWehJoDWN7WJ2UVC+4EWU+/E:MSHmsm1b34VUWU1
Entropy
6.238663
Antivirus
Bitdefender
Gen:Variant.Tedy.146424
Emsisoft
Gen:Variant.Tedy.146424 (B)
ESET
a variant of Win64/Agent.AQS trojan
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
78a926f899....
Dropped
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
Description
This artifact is a DLL that drops and executes a reverse shell utility. When the DLL is loaded it will drop an embedded and base64 encoded payload named ‘xesmartshell’ (508dd87110...) into the path C:\Windows\Temp. The program will then invoke certutil[.]exe with the –decode option and write the new file as xesvrs[.]exe (1fed0766f5...) into C:\Windows\Temp. Cmd[.]exe is then invoked to execute the reverse shell.
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
Tags
backdoordecryptordroppertrojan
Details
Name
XEReverseShell.exe
Size
26624 bytes
Type
PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows
MD5
37e173b932596af62fefc4dc10c8551d
SHA1
342e7fe54de2a60bbb82d29af375385d4ba335fe
SHA256
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
SHA512
d4f823e08ee697d2900ca7efcb6edecb3000a140d90cb20e6ef587d8107e249a01771a783863ab155cec87e082ca57ad84da4b54ecac073a15a3b106933cf43c
ssdeep
768:jEyUcAiat1Nk8JIN9F76BnwRigRI1n4N:AyszWSEigm4N
Entropy
4.348908
Path
C:\Windows\Temp
Antivirus
Avira
HEUR/AGEN.1236126
Bitdefender
Gen:Heur.Bodegun.19
Comodo
Malware
Emsisoft
Gen:Heur.Bodegun.19 (B)
ESET
MSIL/Agent.CYN trojan
IKARUS
Backdoor.MSIL.Bladabindi
K7
Riskware ( 0040eff71 )
McAfee
GenericRXLT-TK!37E173B93259
NANOAV
Trojan.Win32.Generic.htfhkw
VirusBlokAda
TScope.Trojan.MSIL
Zillya!
Trojan.Agent.Win32.1367166
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
815d262d38....
Dropped
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
815d262d38....
Dropped_By
78a926f899320ee6f05ab96f17622fb68e674296689e8649c95f95dade91e933
815d262d38....
Connected_To
xegroups[.]com
Description
This artifact is a reverse shell utility named ‘XE ReverseShell[.]exe’ that is dropped and decoded by "1596686310[.]434117[.]png" (78a926f899...). When the utility is executed it will attempt to connect to the domain xegroups[.]com to obtain the IP address of the C2 and port number to listen on. If no IP address or port number is obtained the program will terminate.
xegroups[.]com
Tags
command-and-control
Ports
HTTP Sessions
GET /masterip HTTP/1[.]1
GET /masterport HTTP/1[.]1
Whois
Domain Name: XEGROUPS[.]COM
Relationships
xegroups[.]com
Resolved_To
184[.]168[.]104[.]171
xegroups[.]com
Connected_From
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
xegroups[.]com
Connected_From
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
Description
At the time of analysis, the files "XEReverseShell[.]exe" (815d262d38...) and "Multi-OS_ReverseShell[.]exe" (1fed0766f56...) attempted to connect to this domain.
508dd87110cb5bf5d156a13c2430c215035db216f20f546e4acec476e8d55370
Tags
backdoordecryptordownloaderdropperloadertrojan
Details
Name
xesmartshell.tmp
Size
35499 bytes
Type
ASCII text, with very long lines, with no line terminators
MD5
0bcceb4fdfb12db21fdfc3a42b9c4693
SHA1
f57d14e291eba19ce484ec4702a7e1f67eaeb7a0
SHA256
508dd87110cb5bf5d156a13c2430c215035db216f20f546e4acec476e8d55370
SHA512
0734d29669a988680e1fedade894d541e37b301460761e247acaa77265d694c441dbff5dca3c7603a77384a969fdd45e375040c582f2de7479fbbcb105a52e20
ssdeep
768:lcK0h28/Z2uPn9V+58vQK9Pu605OF18oukmsuH9wuHE2suSxFuPR22p1Ek:lc8k2Y9VN9Pj0UF101Ek
Entropy
4.370109
Path
C:\Windows\Temp
Antivirus
Bitdefender
Gen:Heur.Bodegun.19
Emsisoft
Gen:Heur.Bodegun.19 (B)
IKARUS
Trojan-Downloader.MSIL.Agent
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
508dd87110....
Related_To
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
Description
This artifact is a base64 encoded file. The file will be decoded using the command-line utility certutil[.]exe and executed as xesvrs[.]exe (1fed0766f5...).
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
Tags
backdoordecryptordroppertrojan
Details
Name
xesvrs.exe
Size
30719 bytes
Type
PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows
MD5
d85880ad1e87c4266f899eca02207dd4
SHA1
a7fc982d1fc30548cbe43cf643be22a31323f23b
SHA256
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
SHA512
a16333b864b1ec58db6e3a8bc18c9aa4c09ad71fcbe68054c0bfb6a0c41584750962388b153d72bcb238c2b6d7e14bc5b39af896fecc61ce646443e12369a24e
ssdeep
768:jEyUcAiat1Nk8JIN9F76BnwRigRI1n4Nkn:AyszWSEigm4N+
Entropy
4.381223
Path
C:\Windows\Temp
Antivirus
Avira
HEUR/AGEN.1236126
Bitdefender
Gen:Heur.Bodegun.19
Emsisoft
Gen:Heur.Bodegun.19 (B)
ESET
MSIL/Agent.CYN trojan
K7
Riskware ( 0040eff71 )
McAfee
GenericRXLT-TK!D85880AD1E87
VirusBlokAda
TScope.Trojan.MSIL
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
1fed0766f5....
Dropped
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
1fed0766f5....
Related_To
508dd87110cb5bf5d156a13c2430c215035db216f20f546e4acec476e8d55370
1fed0766f5....
Related_To
d9273a16f979adee1afb6e55697d3b7ab42fd75051786f8c67a6baf46c4c19c2
1fed0766f5....
Connected_To
xegroups[.]com
Description
This artifact is a reverse shell utility named ‘Multi-OS ReverseShell[.]exe’ that is decoded from xesmartshell[.]tmp (508dd87110...). When the utility is executed it will attempt to connect to the domain xegroups[.]com using Secure Sockets Layer (SSL) to obtain the IP address of the C2 and port number to listen on. If no IP address or port number is obtained the program will terminate.
e45ad91f12188a7c3d4891b70e1ee87a3f23eb981804ea72cd23f1d5e331ff5a
Tags
decryptordroppertrojan
Details
Name
1596835329.5015914.png
Size
165888 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
137423d7b7f5a5684a9b1457f46fdfb2
SHA1
679a6b4b7fa0978e38b327e318059c26b883b064
SHA256
e45ad91f12188a7c3d4891b70e1ee87a3f23eb981804ea72cd23f1d5e331ff5a
SHA512
d56ed37959b6ea37d0f2e58d6f1f61b7b85fa593d1228a402c9798c945e52432008c7a897a6b8e40bfd33fae22df34db93ce46a83f728675e109d828bc1cb995
ssdeep
3072:orofuzXob2OYWWibJXDYipzo2UVX+pnn/quS/eSzYU:FfuzXZOY3aSinn/quS/eSz
Entropy
6.244787
Antivirus
Bitdefender
Gen:Variant.Tedy.146424
Emsisoft
Gen:Variant.Tedy.146424 (B)
ESET
a variant of Win64/Agent.AQS trojan
K7
Trojan ( 0058b2b81 )
McAfee
RDN/Generic Exploit
Zillya!
Trojan.Agent.Win64.22713
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
e45ad91f12....
Related_To
d9273a16f979adee1afb6e55697d3b7ab42fd75051786f8c67a6baf46c4c19c2
e45ad91f12....
Dropped
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
Description
This artifact is a DLL that drops and executes a reverse shell utility. When the DLL is loaded it will drop an embedded and base64 encoded payload named ‘SortVistaCompat’ (d9273a16f9...) into the path C:\Windows\Temp. The program will then invoke the command-line utility certutil[.]exe with the –decode option and write the new file as xesvrs[.]exe (1fed0766f5...) into C:\Windows\Temp. Cmd[.]exe is then invoked to execute the dropped file.
d9273a16f979adee1afb6e55697d3b7ab42fd75051786f8c67a6baf46c4c19c2
Tags
backdoordroppertrojan
Details
Name
SortVistaCompat
Size
36183 bytes
Type
ASCII text, with very long lines, with no line terminators
MD5
42d7b2e1bcf75f9c469afa340f078c86
SHA1
490a804022bcf79688422821df6012c429cec391
SHA256
d9273a16f979adee1afb6e55697d3b7ab42fd75051786f8c67a6baf46c4c19c2
SHA512
127f3a7d8a74d6dcbb400313d305ac228be42a55a07c17af4d1243e6797b3059bde5590953616f8715a9fa1ec11ebfa94de9d7413c14c9c6d6b0a5d5b65dc091
ssdeep
768:7inoJ6DKT4LxIgO2xl7wZLLbuM33kIBn37/vSHpaTNu8ETudlSCusxJ5caWYGx3c:OnoJe+gO2xJKuMnkCnz6HUTCJSTJ
Entropy
4.388474
Path
C:\Windows\Temp
Antivirus
Bitdefender
Gen:Heur.Bodegun.19
Comodo
Malware
Emsisoft
Gen:Heur.Bodegun.19 (B)
IKARUS
Trojan.MSIL.Agent
NANOAV
Trojan.Win32.Generic.hthjis
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
d9273a16f9....
Related_To
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
d9273a16f9....
Related_To
e45ad91f12188a7c3d4891b70e1ee87a3f23eb981804ea72cd23f1d5e331ff5a
Description
This artifact is a base64 encoded file. The file will be decoded using the command-line utility certutil[.]exe and executed as xesvrs[.]exe (1fed0766f5...).
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
Tags
backdoordecryptordroppertrojan
Details
Name
Multi-OS_ReverseShell.exe
Size
27136 bytes
Type
PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows
MD5
f968639a4840535a6ecda1cbe3065260
SHA1
7d6a87fa147d36ec7c46fddbb42ba7665f502207
SHA256
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
SHA512
80a5b1054a7efc7fd7a98a3b13ec13d806f9c7a421f61300812799a87a9f4f96059db54a9318b382d4a4f71364944e2bb1a45af946b1965f056f6a4bad37c6d1
ssdeep
768:zwEtSNcAiat1Nk8JIN9F76BnwRigRI1terN:zfA/zWSEig1rN
Entropy
4.404027
Path
C:\Windows\Temp
Antivirus
Avira
HEUR/AGEN.1236126
Bitdefender
Gen:Heur.Bodegun.19
Emsisoft
Gen:Heur.Bodegun.19 (B)
ESET
a variant of MSIL/Agent.CYN trojan
IKARUS
Backdoor.MSIL.Bladabindi
K7
Riskware ( 0040eff71 )
McAfee
GenericRXLT-TK!F968639A4840
NANOAV
Trojan.Win32.Generic.hthjis
Trend Micro
Backdoo.52B82A20
Trend Micro HouseCall
Backdoo.52B82A20
VirusBlokAda
TScope.Trojan.MSIL
Zillya!
Trojan.Agent.Win32.1371723
YARA Rules
rule CISA_10413062_10 : XEReverseShell trojan backdoor downloader dropper webshell remote_access communicates_with_C2 exfiltrates_data installs_other_components
ssdeep Matches
No matches found.
Relationships
a0ab222673....
Dropped
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
a0ab222673....
Dropped_By
e45ad91f12188a7c3d4891b70e1ee87a3f23eb981804ea72cd23f1d5e331ff5a
a0ab222673....
Connected_To
xework[.]com
Description
This artifact is a reverse shell utility named ‘XEReverseShell[.]exe’ that is dropped by "1596835329[.]5015914[.]png" (e45ad91f12...) into C:\Windows\Temp as xesvrs[.]exe. When the utility is executed it will attempt to connect to the domain xework[.]com to obtain the IP address of the C2 and port number to listen on. If no IP address or port number is obtained the program will terminate.
11415ac829c17bd8a9c4cef12c3fbc23095cbb3113c89405e489ead5138384cd
Tags
downloadertrojan
Details
Name
1597974061.4531896.png
Size
92160 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
bf6722f2055b13a61dfb7233af8d966a
SHA1
161435d198f3dba6ac1ce045b73ccd61f7697146
SHA256
11415ac829c17bd8a9c4cef12c3fbc23095cbb3113c89405e489ead5138384cd
SHA512
dc5dda0aab59c95af5d01b8491b428eee21a62fe1381d85a6faa0caf5d0a3022bcc02777d88b59cda304d57cac1308fdd6676d8040b618e76f28e05d1903c8ad
ssdeep
1536:P6qfkBhbpqNOQiazS7pG5lnMnoJSsFnJ5yvd2+D5lUBHTyRcf01sW7d09dlmv5fB:P6qMfbM88zCpuNMnoDByvd2+D5lUBHTJ
Entropy
5.822163
Antivirus
AhnLab
Malware/Win.Generic
Avira
TR/Agent.brfsc
Bitdefender
Gen:Variant.Tedy.146424
Emsisoft
Gen:Variant.Tedy.146424 (B)
ESET
a variant of Win64/Agent.AQS trojan
IKARUS
Trojan.Win64.Agent
K7
Trojan ( 0057f7991 )
Zillya!
Trojan.Agent.Win64.8597
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
11415ac829....
Connected_To
hivnd[.]com
Description
This artifact is a DLL that is designed to invoke PowerShell to download and execute a file on the system. When the DLL is executed it will attempt to connect to the Uniform Resource Locator (URL) hivnd[.]com/thumpxcache and download a file to the path C:\Windows\Temp. The downloaded file is named thumcache[.]exe and is invoked using cmd[.]exe[.]
hivnd[.]com
Tags
command-and-control
URLs
hxxps://hivnd[.]com/thumpxcache
Ports
Whois
Domain Name: HIVND[.]COM
Relationships
hivnd[.]com
Connected_From
11415ac829c17bd8a9c4cef12c3fbc23095cbb3113c89405e489ead5138384cd
hivnd[.]com
Resolved_To
184[.]168[.]104[.]171
Description
At the time of analysis, the file "1594142927[.]995679[.]png" (11415ac829...) attempted to connect to this domain.
72f7d4d3b9d2e406fa781176bd93e8deee0fb1598b67587e1928455b66b73911
Tags
trojan
Details
Name
1594142927.995679.png
Size
90624 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
15abeb0916a402a107c401056ebf5ac6
SHA1
6b2cf97aa2adb09badbe571a4ff93bcd2398c399
SHA256
72f7d4d3b9d2e406fa781176bd93e8deee0fb1598b67587e1928455b66b73911
SHA512
6c1cae131f77043c2f53347f0eccc010e7178ed11735cf385e8d94c065c63026a6b2c82c4aafc57f9ea1a244963c0c5fc3e898655cc6e208d3c03ebed372564e
ssdeep
1536:gZ+EwudBL87aSQH7HfVf2oNkJ+aNIuTJ1ExXDihMvE00sWhd09dlunB:W+EwQLUa1H7Nf2oW7NIuTJ1ExXDihMvQ
Entropy
5.842722
Antivirus
Avira
HEUR/AGEN.1251118
Bitdefender
Gen:Variant.Tedy.146424
Emsisoft
Gen:Variant.Tedy.146424 (B)
ESET
a variant of Win64/Agent.ASC trojan
IKARUS
Trojan.Win64.Agent
K7
Trojan ( 00580e951 )
Zillya!
Trojan.Agent.Win64.10088
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Description
This artifact is a DLL that is designed to download and execute a payload. The file does not contain a URL to check for downloads. If the program determines that it is running in a virtual environment, it will trigger an exception and terminate.
833e9cf75079ce796ef60fc7039a0b098be4ce8d259ffa53fe2855df110b2e5d
Tags
trojan
Details
Name
1665128935.8063045.dll
Size
118784 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
cf96a7d57a2e28c288c75d371ca06f19
SHA1
f2dee8aa01f39543abe8d887cdeb301aa6a13088
SHA256
833e9cf75079ce796ef60fc7039a0b098be4ce8d259ffa53fe2855df110b2e5d
SHA512
6e1d4476363b75c35db705f6ae73cd6d9f6da410a120aa3d8fd5a92fb84c5d78739e84c9f4c8385ddf0e766052627b0b50143253eae839e6e1922f22ab955ab0
ssdeep
1536:oUhdTegMhxsGrNzpZjh4E5F/693uSV81fm2jMuq/I4Jll6VsWDLdP9dlz+sTepP:bXTgIWpZSEfC+Q81O2jM/w4tsvZE
Entropy
6.102716
Antivirus
ESET
a variant of Win64/Agent.ASC trojan
McAfee
GenericRXLC-WC!CF96A7D57A2E
YARA Rules
rule CISA_10413062_13 : wiper information_gathering
ssdeep Matches
No matches found.
Relationships
833e9cf750....
Connected_To
137[.]184[.]130[.]162
Description
This file is a .NET DLL, which contains malicious unmanaged 64-bit Intel code. This DLL deletes .dll files ending with ".dll" extension in the "C:\windows\temp" directory on the infected machine. This sample also has the capability to enumerate the system, get network parameters including host name, domain name, Domain Name System (DNS) servers, NetBIOS ID, adapter information, IP address, subnet, gateway IP, and Dynamic Host Configuration Protocol (DHCP) server. The sample then communicates the collected data to a C2 server located at IP address 137[.]184[.]130[.]162.
137[.]184[.]130[.]162
Tags
command-and-control
Ports
Whois
NetRange: 137[.]184[.]0[.]0 - 137[.]184[.]255[.]255
Relationships
137[.]184[.]130[.]162
Connected_From
833e9cf75079ce796ef60fc7039a0b098be4ce8d259ffa53fe2855df110b2e5d
137[.]184[.]130[.]162
Connected_From
b4222cffcdb9fb0eda5aa1703a067021bedd8cf7180cdfc5454d0f07d7eaf18f
137[.]184[.]130[.]162
Connected_From
707d22cacdbd94a3e6dc884242c0565bdf10a0be42990cd7a5497b124474889b
137[.]184[.]130[.]162
Connected_From
74544d31cbbf003bc33e7099811f62a37110556b6c1a644393fddd0bac753730
137[.]184[.]130[.]162
Connected_From
f5cafe99bccb9d813909876fa536cc980c45687d0f411c5f4b5346dcf6b304e4
137[.]184[.]130[.]162
Connected_From
dedf082f523dfcb75dee0480a2d8a087e3231f89fa34fcd2b7f74866a7b6608f
Description
This IP address is the C2 server that the samples connect to.
b4222cffcdb9fb0eda5aa1703a067021bedd8cf7180cdfc5454d0f07d7eaf18f
Tags
trojan
Details
Name
1665129315.9536858.dll
Size
92672 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
fdef4ea27c8634c9aa94f1a16844d62c
SHA1
e12c91e1f30740ed95b9a005c8d7bd17c57d0665
SHA256
b4222cffcdb9fb0eda5aa1703a067021bedd8cf7180cdfc5454d0f07d7eaf18f
SHA512
20898eaa33a893dde2bde5f58673ca9795019133150b3d5f201a20d0f28e0f4e9606f19ed2e96181a28e58ff4ba9f52609f0f6326b94570a29c1ed1af3e95f25
ssdeep
1536:26rED/9NI76mpDrAXUSH/jJKIRYgg7SIJQwKsW+bd09dlfXBm:brEb9NInpDUEa/joaYgguIewRxMVx
Entropy
5.853133
Antivirus
Avira
HEUR/AGEN.1251118
Bitdefender
Gen:Variant.Cerbu.106114
Emsisoft
Gen:Variant.Cerbu.106114 (B)
ESET
a variant of Win64/Agent.AQS trojan
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
b4222cffcd....
Connected_To
137[.]184[.]130[.]162
Description
This file is a .NET DLL, which contains malicious unmanaged 64-bit Intel code. This sample has the capability to load additional libraries, enumerate the system, processes, files, directories, and has the ability to write files, get network parameters including host name, domain name, DNS servers, NetBIOS ID, adapter information, IP address, subnet, gateway IP, and DHCP server. The sample then communicates the collected data to a C2 server located at IP address 137[.]184[.]130[.]162.
707d22cacdbd94a3e6dc884242c0565bdf10a0be42990cd7a5497b124474889b
Tags
trojan
Details
Name
1665130178.9134793.dll
Size
94208 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
98b513886879300679d634fa4e1cd27e
SHA1
e1bb93514f221e5c7ab14eb7793eebd4b10c9008
SHA256
707d22cacdbd94a3e6dc884242c0565bdf10a0be42990cd7a5497b124474889b
SHA512
524d38ff7936f5c509b67099d1a2e04e0869a9e3431a1901cfe6720112e77ac01e3d94812a7ee7b82b09c31ee0b101ff2a7e68bc7504a7ab8cd9f84ba719e931
ssdeep
1536:3siPxIb5AVc+gmXSrCbKChSw9mgMNFl276Jw9UsWtBd09dl+7BnA2oHO:DpIN3+7XzbBh9xMbl2m2907MgVnAY
Entropy
5.868150
Antivirus
Avira
HEUR/AGEN.1251118
ESET
a variant of Win64/Agent.ASC trojan
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
707d22cacd....
Connected_To
137[.]184[.]130[.]162
Description
This file is a .NET DLL, which contains malicious unmanaged 64-bit Intel code. This sample has capability to get network parameters including host name, domain name, DNS servers, NetBIOS ID, adapter information, IP address, subnet, gateway IP, DHCP server, and additional data and communicate it to a C2 server located at IP address 137[.]184[.]130[.]162 over port 443.
74544d31cbbf003bc33e7099811f62a37110556b6c1a644393fddd0bac753730
Tags
trojan
Details
Name
1665131078.6907752.dll
Size
117248 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
c1127046e07137180c41cc1914e52ee7
SHA1
7b195c18042ab5c3ed9ebdc66800aec39e29f726
SHA256
74544d31cbbf003bc33e7099811f62a37110556b6c1a644393fddd0bac753730
SHA512
eab5832db04ad82eb07364e743d4506e5511937bd5f4c7b4d6383ec88df5a20b70f228382ccffd64b005e8b186cdef7d7cd138144a8f9a434594069c49c84434
ssdeep
3072:rPMMU3GQDizMxtgk3KeJwbUyS6zt1vaefUP:82QoeguKS/y/0
Entropy
6.082096
Antivirus
Avira
HEUR/AGEN.1229794
ESET
a variant of Win64/Agent.AQS trojan
McAfee
GenericRXLC-WC!C1127046E071
YARA Rules
rule CISA_10413062_13 : wiper information_gathering
ssdeep Matches
No matches found.
Relationships
74544d31cb....
Connected_To
137[.]184[.]130[.]162
Description
This file is a .NET DLL, which contains malicious unmanaged 64-bit Intel code. This file has the same functionality as the file "1665128935[.]8063045[.]dll" (833e9cf750...).
f5cafe99bccb9d813909876fa536cc980c45687d0f411c5f4b5346dcf6b304e4
Tags
trojan
Details
Name
1665132690.6040645.dll
Size
117248 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
75221233a7dd7c5084a7d57084fd8d43
SHA1
5ca0fcea7c0a4e12081cc5848ea74fd7933c599c
SHA256
f5cafe99bccb9d813909876fa536cc980c45687d0f411c5f4b5346dcf6b304e4
SHA512
2e35304a354cf3737b6ff21a78f71005cb7143a8284fc0155cdd793edd206c48bbe89f02f035cd960d49cd6e9877077a90b0bacda6cafd880be0a95042223577
ssdeep
3072:ruNzEKGfQiGhdpWrb0k9b5i9qzt1vB+FUe:3XfspYbdiY+
Entropy
6.083139
Antivirus
Avira
HEUR/AGEN.1229794
ESET
a variant of Win64/Agent.AQS trojan
McAfee
GenericRXLC-WC!75221233A7DD
YARA Rules
rule CISA_10413062_13 : wiper information_gathering
ssdeep Matches
No matches found.
Relationships
f5cafe99bc....
Connected_To
137[.]184[.]130[.]162
Description
This file is a .NET DLL, which contains malicious unmanaged 64-bit Intel code. This file has the same functionality as the file "1665128935[.]8063045[.]dll" (833e9cf750...).
dedf082f523dfcb75dee0480a2d8a087e3231f89fa34fcd2b7f74866a7b6608f
Tags
trojan
Details
Name
1665214140.9324195.dll
Size
115200 bytes
Type
PE32+ executable (DLL) (GUI) x86-64 Mono/.Net assembly, for MS Windows
MD5
ded299dfdd68608084b8183c6d48b7a5
SHA1
7d165f6029eae067785fdb9af53385170d790e52
SHA256
dedf082f523dfcb75dee0480a2d8a087e3231f89fa34fcd2b7f74866a7b6608f
SHA512
29a1aef7393f2bdea60cbc69b50506ec1ee23f862b3856e4469385dfa7fd47e38d6ad7fb746fde8e6f1f9a74d309552b1dab3896d5c60fc14ba87d6ee32331ac
ssdeep
1536:rEFL/kVxbrRMgcfPJR8ba2kV9AuSv/W7eNoFhJlDsW9dP9dlDw0Ve:gF8zr/KJR8D09He/W7eN8hVvNw1
Entropy
6.080040
Antivirus
Avira
HEUR/AGEN.1229794
ESET
a variant of Win64/Agent.ASC trojan
McAfee
GenericRXLC-WC!DED299DFDD68
YARA Rules
rule CISA_10413062_13 : wiper information_gathering
ssdeep Matches
No matches found.
Relationships
dedf082f52....
Connected_To
137[.]184[.]130[.]162
Description
This file is a .NET DLL, which contains malicious unmanaged 64-bit Intel code. This file has the same functionality as the file "1665128935[.]8063045[.]dll" (833e9cf750...), except it does not have the capability for network communication. However, the IP address 137[.]184[.]130[.]164 is hard-coded within the sample like the other files.
Relationship Summary
e044bce06e....
Connected_To
45[.]77[.]212[.]12
45[.]77[.]212[.]12
Connected_From
e044bce06ea49d1eed5e1ec59327316481b8339c3b6e1aecfbb516f56d66e913
45[.]77[.]212[.]12
Connected_From
d69ac887ecc2b714b7f5e59e95a4e8ed2466bed753c4ac328931212c46050b35
45[.]77[.]212[.]12
Connected_From
853e8388c9a72a7a54129151884da46075d45a5bcd19c37a7857e268137935aa
45[.]77[.]212[.]12
Connected_From
a14e2209136dad4f824c6f5986ec5d73d9cc7c86006fd2ceabe34de801062f6b
d69ac887ec....
Connected_To
45[.]77[.]212[.]12
853e8388c9....
Connected_To
45[.]77[.]212[.]12
a14e220913....
Connected_To
45[.]77[.]212[.]12
8a5fc2b8ec....
Dropped
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
11d8b9be14....
Dropped_By
8a5fc2b8ecb7ac6c0db76049d7e09470dbc24f1a90026a431285244818866505
11d8b9be14....
Downloaded
5cbba90ba539d4eb6097169b0e9acf40b8c4740a01ddb70c67a8fb1fc3524570
11d8b9be14....
Connected_To
xework[.]com
xework[.]com
Connected_From
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
xework[.]com
Connected_From
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
xework[.]com
Resolved_To
184[.]168[.]104[.]171
xework[.]com
Resolved_To
144[.]96[.]103[.]245
184[.]168[.]104[.]171
Resolved_To
xegroups[.]com
184[.]168[.]104[.]171
Resolved_To
hivnd[.]com
184[.]168[.]104[.]171
Resolved_To
xework[.]com
144[.]96[.]103[.]245
Resolved_To
xework[.]com
5cbba90ba5....
Related_To
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
5cbba90ba5....
Downloaded_By
11d8b9be14097614dedd68839c85e3e8feec08cdab675a5e89c5b055a6a68bad
08375e2d18....
Related_To
5cbba90ba539d4eb6097169b0e9acf40b8c4740a01ddb70c67a8fb1fc3524570
08375e2d18....
Dropped_By
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
08375e2d18....
Dropped_By
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
08375e2d18....
Dropped_By
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
78a926f899....
Dropped
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
815d262d38....
Dropped
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
815d262d38....
Dropped_By
78a926f899320ee6f05ab96f17622fb68e674296689e8649c95f95dade91e933
815d262d38....
Connected_To
xegroups[.]com
xegroups[.]com
Resolved_To
184[.]168[.]104[.]171
xegroups[.]com
Connected_From
815d262d38a26d5695606d03d5a1a49b9c00915ead1d8a2c04eb47846100e93f
xegroups[.]com
Connected_From
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
508dd87110....
Related_To
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
1fed0766f5....
Dropped
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
1fed0766f5....
Related_To
508dd87110cb5bf5d156a13c2430c215035db216f20f546e4acec476e8d55370
1fed0766f5....
Related_To
d9273a16f979adee1afb6e55697d3b7ab42fd75051786f8c67a6baf46c4c19c2
1fed0766f5....
Connected_To
xegroups[.]com
e45ad91f12....
Related_To
d9273a16f979adee1afb6e55697d3b7ab42fd75051786f8c67a6baf46c4c19c2
e45ad91f12....
Dropped
a0ab222673d35d750a0290db1b0ce890b9d40c2ab67bfebb62e1a006e9f2479c
d9273a16f9....
Related_To
1fed0766f564dc05a119bc7fa0b6670f0da23504e23ece94a5ae27787b674cd2
d9273a16f9....
Related_To
e45ad91f12188a7c3d4891b70e1ee87a3f23eb981804ea72cd23f1d5e331ff5a
a0ab222673....
Dropped
08375e2d187ee53ed263ee6529645e03ead1a8e77afd723a3e0495201452d415
a0ab222673....
Dropped_By
e45ad91f12188a7c3d4891b70e1ee87a3f23eb981804ea72cd23f1d5e331ff5a
a0ab222673....
Connected_To
xework[.]com
11415ac829....
Connected_To
hivnd[.]com
hivnd[.]com
Connected_From
11415ac829c17bd8a9c4cef12c3fbc23095cbb3113c89405e489ead5138384cd
hivnd[.]com
Resolved_To
184[.]168[.]104[.]171
833e9cf750....
Connected_To
137[.]184[.]130[.]162
137[.]184[.]130[.]162
Connected_From
833e9cf75079ce796ef60fc7039a0b098be4ce8d259ffa53fe2855df110b2e5d
137[.]184[.]130[.]162
Connected_From
b4222cffcdb9fb0eda5aa1703a067021bedd8cf7180cdfc5454d0f07d7eaf18f
137[.]184[.]130[.]162
Connected_From
707d22cacdbd94a3e6dc884242c0565bdf10a0be42990cd7a5497b124474889b
137[.]184[.]130[.]162
Connected_From
74544d31cbbf003bc33e7099811f62a37110556b6c1a644393fddd0bac753730
137[.]184[.]130[.]162
Connected_From
f5cafe99bccb9d813909876fa536cc980c45687d0f411c5f4b5346dcf6b304e4
137[.]184[.]130[.]162
Connected_From
dedf082f523dfcb75dee0480a2d8a087e3231f89fa34fcd2b7f74866a7b6608f
b4222cffcd....
Connected_To
137[.]184[.]130[.]162
707d22cacd....
Connected_To
137[.]184[.]130[.]162
74544d31cb....
Connected_To
137[.]184[.]130[.]162
f5cafe99bc....
Connected_To
137[.]184[.]130[.]162
dedf082f52....
Connected_To
137[.]184[.]130[.]162
Recommendations
CISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization's systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
Maintain up-to-date antivirus signatures and engines.
Keep operating system patches up-to-date.
Disable File and Printer sharing services. If these services are required, use strong passwords or Active Directory authentication.
Restrict users' ability (permissions) to install and run unwanted software applications. Do not add users to the local administrators group unless required.
Enforce a strong password policy and implement regular password changes.
Exercise caution when opening e-mail attachments even if the attachment is expected and the sender appears to be known.
Enable a personal firewall on agency workstations, configured to deny unsolicited connection requests.
Disable unnecessary services on agency workstations and servers.
Scan for and remove suspicious e-mail attachments; ensure the scanned attachment is its "true file type" (i.e., the extension matches the file header).
Monitor users' web browsing habits; restrict access to sites with unfavorable content.
Exercise caution when using removable media (e.g., USB thumb drives, external drives, CDs, etc.).
Scan all software downloaded from the Internet prior to executing.
Maintain situational awareness of the latest threats and implement appropriate Access Control Lists (ACLs).
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, "Guide to Malware Incident Prevention & Handling for Desktops and Laptops".
Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/
Document FAQ
What is a MIFR? A Malware Initial Findings Report (MIFR) is intended to provide organizations with malware analysis in a timely manner. In most instances this report will provide initial indicators for computer and network defense. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis.
What is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis.
Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Central .
Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA's homepage at www.cisa.gov .
Please share your thoughts. We recently updated our anonymous Product Feedback Survey and we'd welcome your feedback.